Wait until you record in 8k, or use 20 cameras like during a sporting event.
vk6flab
Refer to Ambience Adjustments in your research proposal?
I had no idea, so I looked .. I still have no idea. The dollar numbers tossed around contradict each other and vary wildly, to the point of being absurd.
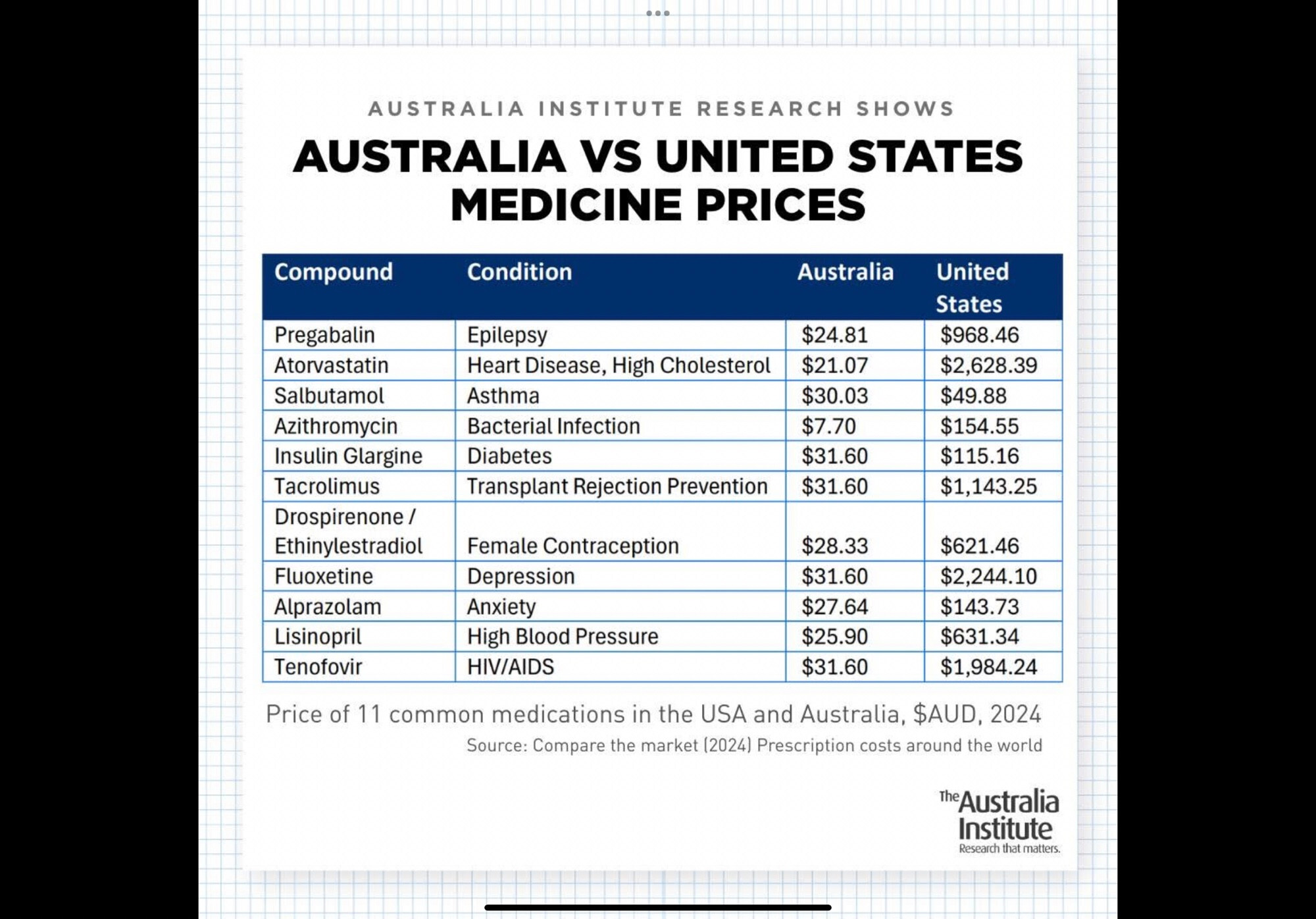
I don't know what the policy on generics is, but as I understand it, the PBS negotiates on our behalf to subsidize medication that would otherwise be completely unaffordable.
When I get to a computer with a screen that's bigger than my hand, I'll have a squiz at the Australian Bureau of Statistics to see if I can learn more.
Edit: Just came across this gem:
They just got fired, together with anyone who might begin to fix this.
Well, kids don't vote, so in his lifetime it's not going to matter to him, which tells you everything you need to know about his policies and political ambitions.
Easy fix.
Hire better negotiators.
Were these idiots dropped on their heads as a baby? In what world can one country dictate the laws of another country without there being a war?
They're trying it on here in Australia too. The USA pharmaceutical industry is lobbying the USA administration by claiming that our PBS, Pharmaceutical Benefits Scheme, which allows us to have affordable medication and a safety net, is harming their bottom line because they're required to negotiate with the Australian Government in order to supply their medication at a negotiated price. Must be tough to have to negotiate with adults.
Rant:
to speak, write or shout in a loud, uncontrolled, or angry way
Source: https://dictionary.cambridge.org/dictionary/english/rant
That's interesting. The Encyclopaedia Britannica appears to contradict this, stating:
However, there doesn’t seem to be much evidence in reference sources to support this theory.
Source: see the reply by @[email protected] to you.
Record it to local storage and use VLC?