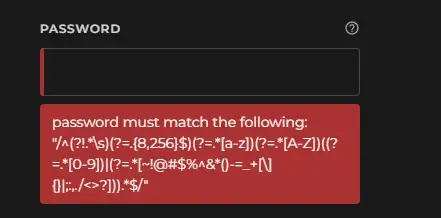
password must be valid regex
Software Gore
A community for posting software malfunctions
Deliberately bad software or bad design is not software gore, it must be something unintentional
Icon base by Delapouite under CC BY 3.0 with modifications to add a gradient and shear it
Those (?=...) bits are positive lookahead assertions:
Lookaround assertions are zero-width patterns which match a specific pattern without including it in $&. Positive assertions match when their subpattern matches, negative assertions match when their subpattern fails. Lookbehind matches text up to the current match position, lookahead matches text following the current match position.
The one (?!...) is a negative lookahead assertion.
The $& var doesn't really matter outside of Perl. It contains the text of the pattern you just matched, but even within Perl, capture groups are preferred. Once used at all, it will slow down your program every time a new regex is hit, which is especially bad in long running web server environments. Gets used sometimes in short scripts, though.
What really matters is that the lookaheads don't consume any text. In other words, the pointer that shows where in the text we are doesn't increment; once we're outside of the lookahead, we're still right back in the same place.
So let's break this down using the /x modifier to make it somewhat sane.
/^
(?!.*\s) # no whitespace allowed
(?=.{8,256}$) # between 8 and 256 characters (the '$' here indicating the end of the string)
(?=.*[a-z]) # has to be a lowercase ASCII alphabet char somewhere
(?=.*[A-Z]) # has to be an uppercase ASCII alphabet char somewhere
( # need a number, or a list of special chars on a US keyboard
(?=.*[0-9])
| (?=.*[~!@#$%^&*()-=_+[\]{}|;:,./<>?])
)
.* # consumes the whole string
$/x
Notes:
- Doesn't make any allowances for non-English characters, or even non-US characters (like the "£" character in the UK)
- There's a whole slew of utf8 characters out there that should count towards "special characters", but aren't considered here
- There's no reason to deny whitespace; let people use passphrases if they want (but then, you also don't want to block those people for not using symbols)
- Putting a limit at 256 is questionable, but may not necessarily be wrong
That last one has some nuance. We often say you shouldn't put any upper limit, but that's generally not true in the real world. You don't want someone flooding an indefinite amount of data into any field, password or not. A large limit like this is defensible.
Also, lots of devs are surprised to learn that bcrypt and scrypt have a length limit of 72 bytes. A way around this is to run your input through SHA256 before giving it to bcrypt or scrypt.
I don't see a reason to limit the length as long as the password hash can handle large values. I am green when it comes to the inner workings of password hashing, so I may be wrong.
Honestly, white space is a character, and adds extra entropy to passwords. I do not understand why people do not want to promote using white space in passwords/passphrases. If I’m missing something intrinsically bad about white space in passwords, I’d love to know.
You're right on. As long as you're otherwise following best practices for storing passwords, there's no downside.
But but but if I add it to the queryparams for my rest endpoint the space will break my URL!
Always urlencode your passwords!
Wait, that doesn't seem right...
When the developer just passes on the js error to the user 👍🏾
I use a password manager with a random password generator. It's always disconcerting when I find a website that finds my passwords to be too complicated. Like "you can't use more than eight characters and the only special characters you can use are @ and !". What the shit?!?
Yeah! Why can't I use a base64 representation of a pirated 4k TS copy of Jon Favreau's "Chef" as my password? /s
Jokes aside, I've heard some hashing algorithms have a high cap of like 20 characters, so developers are probably just too lazy to switch them out or to read the docs on how to properly use said algorithms. Either way it's a very bad sign, maybe just a tad better than them emailing you the password in cleartext.
The worst I have seen recently is one with an eight character limit and support for only four specific special characters. I didn't test if it was cap sensitive but it wouldn't shock me if it was not. It is the invoicing portal for one of my clients. I wish that was the only technical atrocity committed by that abomination...it is not.
My bank used to require internet banking passwords to be exactly 6 alphanumeric characters. Turned out that the reason for that was that they used the same password for internet and phone banking, and by implication the passwords were actually just 6 numbers.
This was in the 2010s, mind you.
Kind of related question: why are no whitespaces allowed in many passwords while special characters are? I'm a huge fan of elaborate nonsense sentence passphrases but get shot down.
(I ask cause that regex has that requirement it seems)
I have no idea if this is true or not but I was told it harkens back to very early multi-user operating systems where user credentials were stored unencrypted in plaintext files that used white space as delimiters.
I tend to believe this might be accurate because I learned programming back in the 1980’s on an Onyx Systems microcomputer. There was a bug that some of us learned about in its rudimentary email program that would dump you into its otherwise-protected system directory. In that directory was a file containing both usernames & passwords in clear text. I don’t recall if it used white space as a delimiter, but given everything was in clear text and not encrypted I think that might have been the case.
Oh boy, having done data science work with government files, you remind me that they still use terrible delimiters. A white space delimiter sounds significantly worse than a tab delimited file, though!