Super cool!
Selfhosted
A place to share alternatives to popular online services that can be self-hosted without giving up privacy or locking you into a service you don't control.
Rules:
-
Be civil: we're here to support and learn from one another. Insults won't be tolerated. Flame wars are frowned upon.
-
No spam posting.
-
Posts have to be centered around self-hosting. There are other communities for discussing hardware or home computing. If it's not obvious why your post topic revolves around selfhosting, please include details to make it clear.
-
Don't duplicate the full text of your blog or github here. Just post the link for folks to click.
-
Submission headline should match the article title (don’t cherry-pick information from the title to fit your agenda).
-
No trolling.
-
No low-effort posts. This is subjective and will largely be determined by the community member reports.
Resources:
- selfh.st Newsletter and index of selfhosted software and apps
- awesome-selfhosted software
- awesome-sysadmin resources
- Self-Hosted Podcast from Jupiter Broadcasting
Any issues on the community? Report it using the report flag.
Questions? DM the mods!
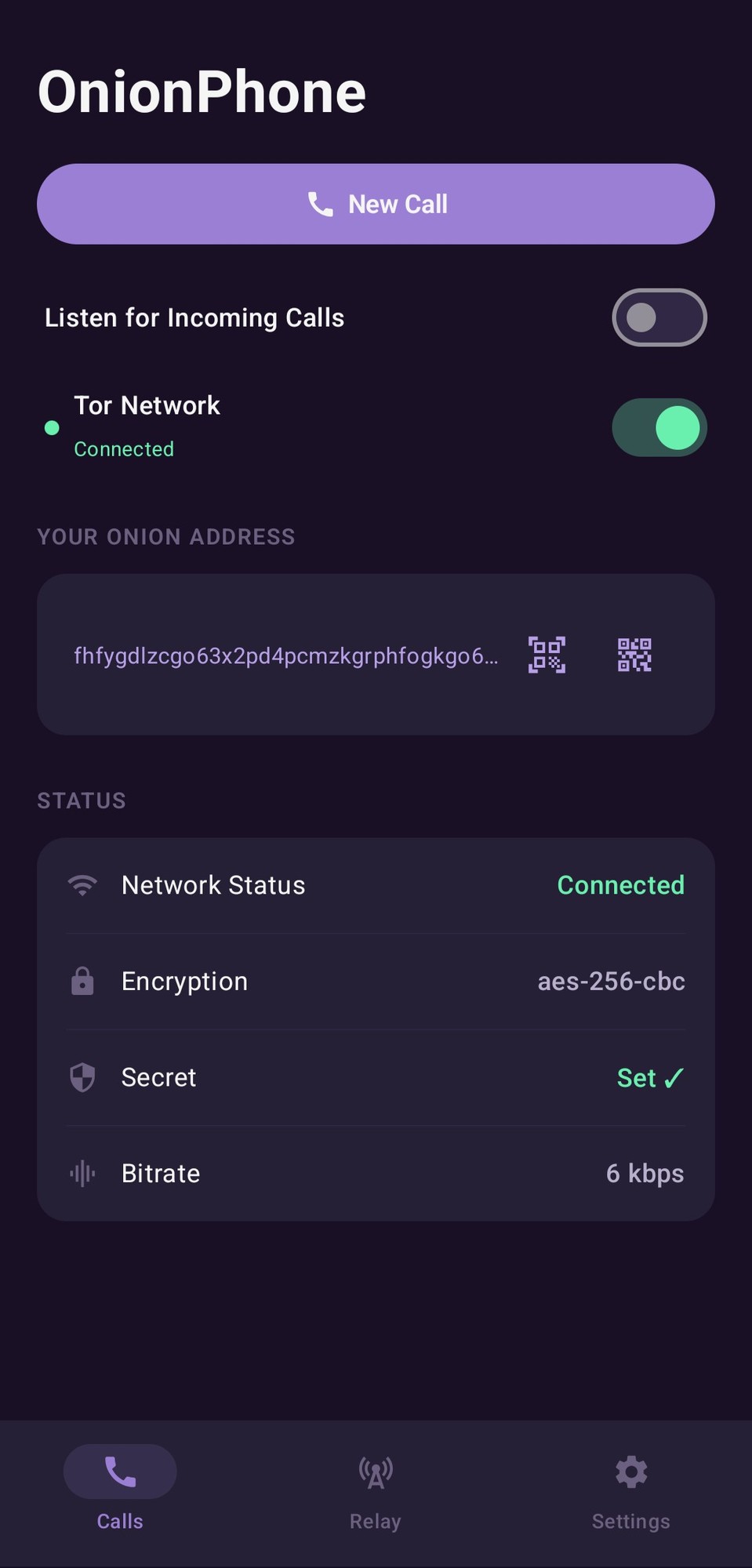
This is extremely cool.
Wow so awesome going to try it out.
Nice a real step forward for private communication.
Would be awesome if it ever has a messaging section without having to make a call, still, an awesome start!
Would be awesome if it ever has a messaging section without having to make a call, still, an awesome start!
convenient in one app, but we already have briar for that
I've put some thought into this. The biggest roadblock to P2P is 24/7 persistence. You have to be online.
I think the most straightforward path to this is having the ability to setup a mailbox sort of how the relay works but on a machine that's on a 24/7 stable connection. Because it's already cross compatible with Linux systems, it would make the most sense to have a dedicated mailbox there, and have it forward your messages that were missed while you were offline.
Once the mailbox is set up, it's just a matter of tieing the separate mailbox identity to forward messages to you once your online. Ideally integrate tors built in authorized client protocol to ensure only one person is authorized to the mailbox.
This is stupidly cool omg
@Used_Gate I suggest getting this in f-droid if you want to see more usage.
Also, it looks like the actual development happens in private and then is thrown over the fence; https://gitlab.com/here/_forawhile/onionphone/-/commit/2c4afc462a42852f0d54dda0b333db9019f3d69e
Yes, I am seeking that out to put it on fdroid and actually tried but ran into a few roadblocks.
I am tracking changes since v1.0.0 in the changelog. From here on out the changes are all public. The initial commit has no history because it was brand new, and the architecture was forked from terminal phone for cross compatibility.
How can I contribute?
I need ideas for what everyone wants. Features and niceties to make the expirence more polished. I have a limited set of devices that I can test on so finding bugs and edge cases is something I can fix, but limited to my environments/devices.
I've played with the ability to have a dedicated secure database built in for contacts but unsure if it's really needed and worth implementing.
Sounds good. I'll pull the latest build to my graphenOS test mule.
I'll target a secured db as a vault for contacts. That's a really good idea.
This is sick! Thanks for sharing your project with us! I would have never guessed you could do voice over TOR but PTT was a clever solution. Its like the old nextel phones that had PTT. I wonder if its possible to remap the volume button to be a hardware PTT button.
Happy to contribute! So, currently (only while in the app for now) you can activate the mic with a double pressdown on volume if the setting is enabled.
My attempts to trigger the mic while outside the app came with a few unwanted side affects so I removed it for now until I find a solid way to do that.
What's the selfhosted component of this?
Self hosting your own private P2P voice service.
Optionally use your device as a Audio relay for group calls, in which case you become the 'server' to all connected clients.
Self hosting [...] P2P
You do realise that's a contradiction, right?
Unless you're hosting a TOR node (which is outside of the scope here and, in the case of exit nodes, extremely risky), there's nothing here that's relevant to self-hosting.
I don't agree with that. Both sides are acting as a server and a client, connecting via a onion service to either parties rendezvous. And then when you include the fact that you can become a relay, that is clearly self hosting a server in a pure sense.
There are no exit nodes involved in onion services. It all stays within the network.
Probably a bad idea to congest the limited bandwidth of Tor with voice chat.
The bandwidth is low by design. I've excluded files and images to keep it down as well. You could talk 24/7 only use MBs.
If we want Tor to grow we need useful applications useful for everyone. I doubt this will be widely adopted.
I've contributed a large amount of bandwidth to the network so why can't I use some?
Creating more mainstream use-cases is how you get people to donate more bandwidth.
Plain speech can be compressed pretty well. I'm not an expert by any means, but I suspect latency would be the bigger issue.
Latency is a huge issue, but it goes away with the PTT model. I tried full duplex on initial prototyping but it was trash.
PTT solves this by simply forcing the listen, digest, then respond. You can expect about 2-3 seconds of delay from when you release the ptt, to when the other side hears it.
Yeah, unless they use specific nodes given by the community, i think it's a bad idea