this post was submitted on 04 May 2026
371 points (99.7% liked)
Privacy
4467 readers
57 users here now
Icon base by Lorc under CC BY 3.0 with modifications to add a gradient
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
Then this is just a whole lot of not much.
Users have been asking Signal to allow accounts to be created without a phone number ever since it was released. I just want to use Signal with my kids who don't have phone numbers, dude. Signal already have usernames and encrypted client-side contacts.. What's the holdup? Why insist a phone number is still required?
They want to be able to link accounts to your identity, obviously
You know, I've been thinking...
Signal's end to end encrypted, yes... But we do the key exchange process through Signal's servers, don't we? How do we know they don't store copies of the keys? Does the client have a mechanism in place to make sure the man in the middle doesn't do anything funny? I haven't actually delved very deep into the code, but it sounds like I should.
And... Sure, their server code may be open source too, but nobody guarantees that that's the code actually running on their servers.
Here is an overview of all audits done on Signal:
https://community.signalusers.org/t/overview-of-third-party-security-audits/13243
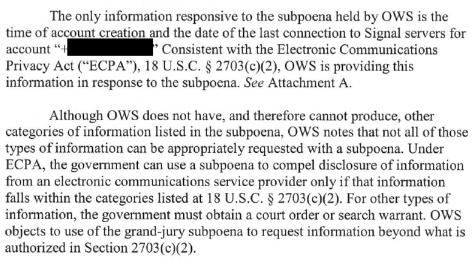
No recent server audits really. They are pretty public about information requests made by the government and their responses though, and from what I can see the only pieces of information they have shared with the government to this point are the time of account creation and the date of the last connection to Signal servers:
You can check more of their responses from here:
https://signal.org/bigbrother/
I don't know how Signal is built, but you can establish a secure communication channel through a channel that's being listened in on, meaning the server doesn't need to ever see the keys. Look up Diffie-Hellman for an example, an algorithm that lets two actors establish a shared secret without communicating enough information to reconstruct the secret.
So if the client uses a secure key exchange algorithm (or straight up asymmetrical encryption) the server can't just grab your keys - you just need a secure way to verify that your keys actually match, because what they could do is a man in the middle attack where they establish a secure channel with you and the person you're messaging, and decrypt and reencrypt messages going both ways, being able to listen in and modify messages.
They ship their app with blobs, so we cannot verify what their app is doing.
My thinking also. Corps/gov can also link identity to emails of course, but it's much harder due to email aliasing and the ease of new account creation.
Mobile phone numbers are far more personal - people generally only have one or two max and generally keep them for very long periods.
If its the true reason, it would make Signal not much better than Meta's WhatsApp, which gleans value from its users by noting metadata tying users to one-another by who they contact, when, and how often to extrapolate social circles and relationships. But Meta goes further in I think also tracking location, etc, and obviously has much more personal data in the linked phone numbers of many FB/Insta accounts.. Signal could potentially be doing some of that to a degree with IP geolocation... Not great.
TLDR: its the one thing stopping me from trusting Signal entirely as a benevolent actor - they want and 'need' your personal phone number. I use it still, as its the best available mainstream option, but I mention this concern when recommending it to those seeking privacy.
For me its the blobs. We can't trust anything they do so long as the code they ship isn't 100% open source
They will also likely require a captcha done using webview, exposing many hardware identifiers to Google.
They will once again claim this is to protect against spammers and not to track people.
Signal is obviously a honeypot, as it never would have taken this long to release a desktop App not linked to a phone if it weren't a honeypot, and they still are requiring a phone number. Any "privacy" company that adopts real privacy features only after huge pushback from the privacy community years later is likely a honeypot. Look at "tuta," which a former government worker testified under oath is a honeypot: no accepting of Monero ever. Finally, when called a honeypot, they make a deal with a third party to accept Monero.
Signal is probably releasing this because whoever owns the honeypot wants to link desktops to phone numbers, allowing the desktops to be hacked with something like Pegasus as well.
Does anyone remember that accidental LinkedIn post showing all the Apps that one company was able to hack? And it showed WhatsApp, Signal, Telegram, etc... And it was always based on a phone? And this photo was accidentally posted online before being scrubbed? I forget the details on it and if anyone remembers, please post about it to jog my memory. Well, now perhaps that group wants to hack laptops too.
I don't believe this is anything other than more bullshit. It wouldn't surprise me if they also blocked VOIP for registration. Fuck Signal.
Extraordinary claims require extraordinary evidence.
The new app design will still be necessary if that were to become a feature, so this is a halfway step either way.
One thing this lets people do is utilize burner numbers without a physical phone tied to it. They can use their provider's web-based UI to receive text messages for the signal confirmation, but can then use the app solely from a desktop.
This also paves the way for an official command-line client, library or SDK that could be used for automation.
Thanks for those pointers. I like the idea of an official CLI for instance to perform automatic regular encrypted backups, or the possibility of interfacing messages to other systems. But I presume they'd have to be careful to avoid opening the door to automated messaging spam bots.
Cause spamming will get a lot worse once you can just register accounts.
This is real false dilemma that people often raise. There's so many tools that Signal can use to stop spam. Do you get spam email? Almost never - even on E2E email, because reputation blacklisting solved it. Signal already only lets accounts message other users in their local contacts list or added by username.
Examples off the top of my head: If a new account is registered it can have a 'gradual release of abilities' whereby it can only send 3 messages first day, 10 first week, etc. Same for adding users by username. Signal already has spam-account reporting capabilities that block accounts after too many reports. Simple. Solved. And the payoff is that everyone gets complete privacy of who they are during signup.
BTW I already get spam on Signal. Here's the latest from just 2 days ago, know nobody by this name and don't recognize her, standard pretty god-botherer bait profile, user photo looks like AI (light reflection left eye very different to right eye):
Require a $15 payment
Then you have the same privacy problem but with payment provider....
For non-phone-numbered accounts
Yep. So.. You sign up with a username, no phone number.. Then you use a payment provider to pay for that account... And.. Your payment info is therefore linked to that account at creation time.
Potential remedy could be using Bitcoin or something as an option, but then.. 99% of people dont have or use crypto, and would just use the default CC/paypal. Same issue.
The fuck do you think the phone number works
You claimed a payment system would solve spam. I explained why that gets right back to the privacy problem.
This has left you deeply confused, apparently. Bye.
I just use SimpleX for kid stuff. No phone/numbers necessary, just uses random QR codes as the identifier, makes sharing and setup very easy.
Oh cool, I'll give this a try, I see it's on IOS also. Cheers